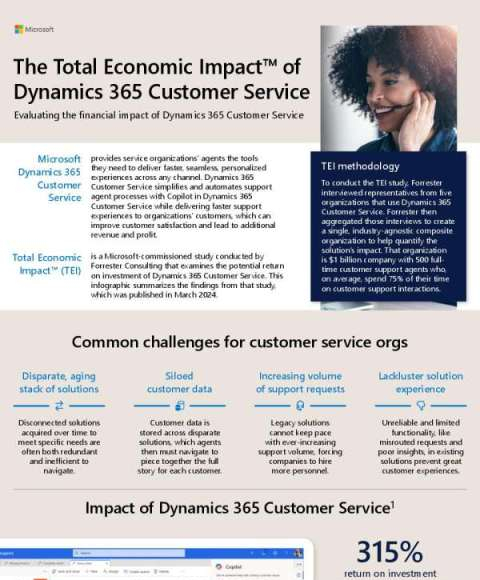
How much could an investment in @Microsoft Dynamics 365 Customer Service impact your bottom-line? Read this Total Economic Impact (TEI) conducted by Forrester Consulting that examines the potential 315% return on investment of Dynamics 365 Customer Service. DM us for an assessment.
Announcing Phi-3 fine-tuning, new generative AI models, and other Azure AI updates to empower organizations to customize and scale AI applications
Developing and deploying AI applications at scale requires a flexible platform that can create solutions grounded in an organization’s organizational data. How would you describe your current AI app process? If there’s room for improvement, take a look at this @Microsoft blog post outlining the new capabilities of the Phi-3 small language models that give your dev teams greater choice and flexibility when creating AI solutions.
The Microsoft Intelligent Data Platform — Unleash your data and accelerate your transformation
Data solutions created today must be designed to ensure they can easily manage spikes in data, new workloads and new technologies for many years to come. How confident are you that your solution can manage future advances? Read this blog about the advantages of the @Microsoft Intelligent Data Platform, the innovative solution that lets you take advantage of integrated advanced analytics and the latest AI tools.
Microsoft named an overall leader in KuppingerCole Leadership Compass for ITDR
Are you looking for the top providers in identity threat detection and response (ITDR)? Microsoft was recently recognized as a leader in ITDR. Read how Microsoft can strengthen your company’s security.
@Microsoft Security
Build and Modernize Intelligent Apps
Organizations interested in making a complete digital transformation know that they need to either modernize their current apps or develop intelligent apps that take advantage of cloud capabilities. How have the modernization plans for your enterprise progressed? If you’d like some help, download this @Microsoft Azure eBook outlining the roadmap that will move your transformation forward.
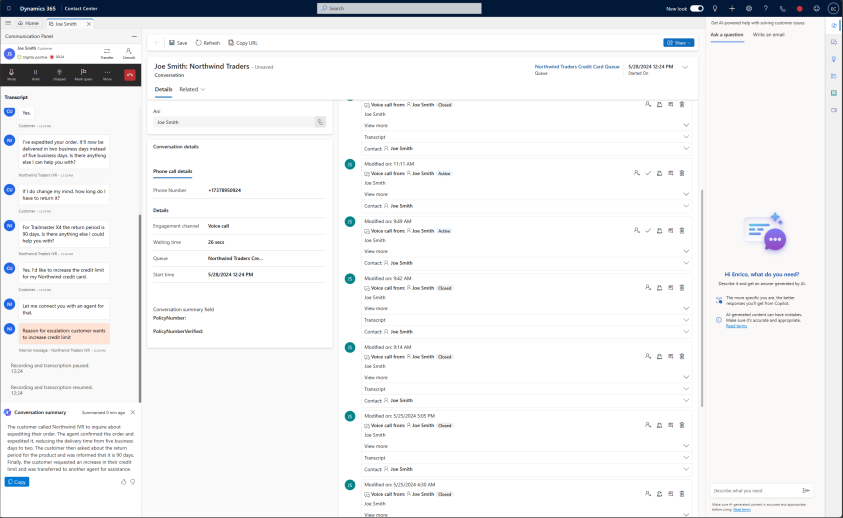
Microsoft Guided Tours
@Microsoft Dynamics 365 Control Center delivers frictionless experiences across channels, reduce call volume and hold times with intelligent chatbots and voicebots, and empower agents to deliver great service where a human touch is required. Take the guided tour to see it in action. DM to discuss putting Dynamics 365 Control Center to work in your organization.
Are you ready to spin up and scale out the modernized apps to drive your business forward? Reply and the Microsoft @Azure experts at ContentMX will be in touch to guide you on the path to app modernization.
Updating your organization’s current apps and data to a cloud-first model is a critical step to your digital transformation. How ready are you for the change? DM to set up a time with the @Microsoft Azure experts at ContentMX who can guide you on the path to app modernization.
Universidad de Las Palmas de Gran Canaria boosts accessibility with Microsoft Entra ID
When the power goes out, does your identity access management service stop working? Protect your cloud applications with Microsoft Entra. Read the case study to learn how one university protects its cloud with Entra.
@Microsoft Security
The Total Economic Impact™ Of Microsoft Entra
Worried about the cost of maintaining your identity and access management (IAM)? @Microsoft Entra can save you money and generate ROI. Get the Forrester report on the total economic impact of Entra with data from Microsoft customers.
@Microsoft Security
Maximizing development with OpenShift Virtualization
The path to modernization can be filled with many roadblocks. How do you get around them? Read this solution brief showing how @Red-Hat OpenShift Virtualization assists your journey using a unified hybrid cloud platform for building, modernizing and deploying applications at scale.